Nursing Paper Example on Fever
Nursing Paper Example on Fever
Fever, or pyrexia, is a temporary elevation in body temperature, often as a result of an infection or other medical condition. Fever is a natural physiological response, triggered by the immune system, to help combat infections. Defined as a body temperature above the normal range of 98.6°F (37°C), fever is commonly recognized at 100.4°F (38°C) or higher. While fever is generally beneficial, helping to reduce the growth of pathogens, high or prolonged fever can be harmful, particularly in vulnerable populations such as infants and elderly individuals. This overview addresses the causes, pathophysiology, types, symptoms, diagnosis, and treatment of fever.

Causes and Pathophysiology
Common Causes of Fever
Fever is often a symptom of an underlying infection, but it can result from a variety of causes, including:
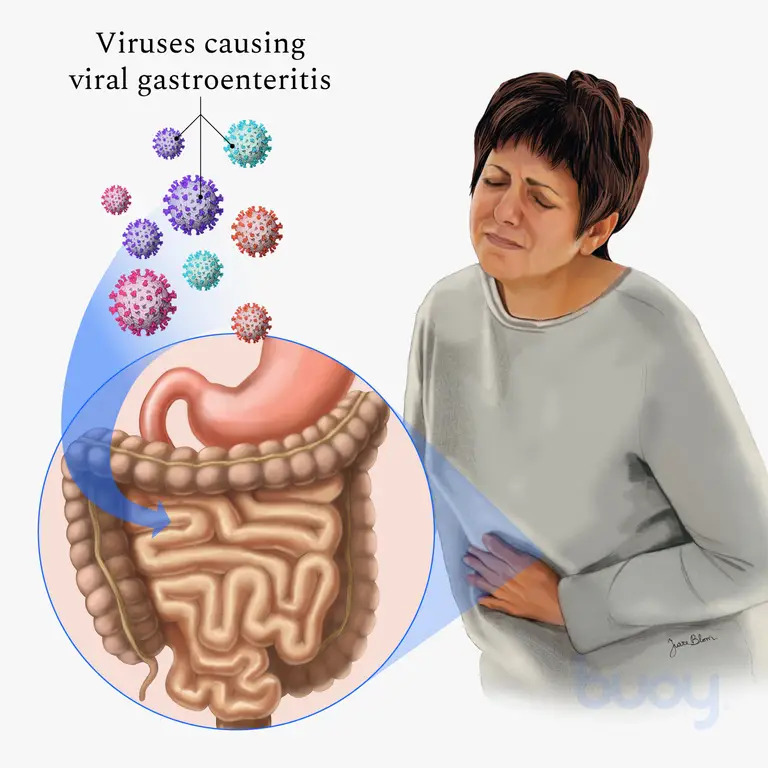
- Infections: Bacterial, viral, fungal, or parasitic infections are primary causes.
- Autoimmune Conditions: Diseases like lupus or rheumatoid arthritis can trigger a fever.
- Inflammatory Disorders: Fever can accompany inflammatory conditions, including inflammatory bowel disease.
- Heat Exhaustion: Prolonged exposure to high temperatures can result in heat-related fever.
- Medication Reaction: Some drugs, such as antibiotics, can cause drug-induced fever.
- Vaccination: Fever may occur as an immune response post-vaccination, typically mild and short-lived.
Pathophysiology of Fever
The pathophysiology of fever involves the hypothalamus, which regulates body temperature. When pyrogens (fever-inducing agents) enter the body, either from external (e.g., bacteria, viruses) or internal sources (e.g., cytokines from the immune system), they stimulate the hypothalamus to raise the body’s set-point temperature. This elevation leads to thermoregulatory adjustments, including shivering and peripheral vasoconstriction, which produce heat and elevate body temperature (Dinarello & Porat, 2020).
Types of Fever
Fever is generally classified based on its pattern and duration:
- Intermittent Fever: Body temperature fluctuates but returns to normal within a 24-hour period, common in diseases like malaria.
- Remittent Fever: Fluctuating temperature that does not return to normal but varies throughout the day, often seen in bacterial infections.
- Sustained or Continuous Fever: The temperature remains elevated with minimal fluctuation, typically associated with infections like typhoid.
- Relapsing Fever: Characterized by recurrent fever episodes, as seen in diseases like Lyme disease and some viral infections (Harrison, 2022).
Symptoms of Fever
Aside from elevated body temperature, symptoms accompanying fever can vary widely:
- Chills and Shivering: Body responses to generate warmth as the temperature rises.
- Sweating: Occurs as fever begins to break or resolve.
- Headache and Muscle Aches: Due to inflammatory responses.
- Fatigue and Weakness: The immune system’s response can cause energy depletion.
- Irritability or Confusion: In children and elderly individuals, fever can lead to changes in behavior or cognition.
These symptoms, however, can vary based on the underlying cause and the patient’s age and overall health condition (Mayo Clinic, 2023).
Diagnosis of Fever
Clinical Assessment
The diagnosis of fever starts with a detailed medical history and physical examination. Healthcare providers assess the pattern, duration, and associated symptoms to identify possible causes.
Temperature Measurement
Measuring body temperature accurately is crucial. Common methods include oral, axillary (underarm), rectal, and tympanic (ear) thermometers. Rectal thermometry is considered the gold standard, especially in infants and children, for accurately detecting fever (Dinarello & Porat, 2020).
Laboratory Tests
When the cause of fever is unclear, additional tests may include:
- Blood Tests: To identify infections or inflammatory markers.
- Urinalysis: To detect urinary tract infections.
- Chest X-ray: If a respiratory infection, like pneumonia, is suspected.
- Cultures: Blood, urine, and other body fluids may be cultured to identify bacterial or fungal infections.
In cases of prolonged or unexplained fever, known as fever of unknown origin (FUO), more extensive testing may be warranted to investigate non-infectious causes (Harrison, 2022).
Treatment and Management
Medication
- Antipyretics: Drugs like acetaminophen and ibuprofen are common choices to lower fever and relieve associated discomfort.
- Antibiotics: Used only if a bacterial infection is confirmed or strongly suspected. Antibiotic use is avoided for viral infections, where supportive care is the primary management.
- Anti-inflammatory Drugs: For fevers due to inflammatory or autoimmune conditions, corticosteroids or nonsteroidal anti-inflammatory drugs may be prescribed.
Supportive Care
- Hydration: Fever increases fluid loss, making adequate hydration essential.
- Rest: Contributes to immune function and speeds recovery.
- Cool Compresses: Can help relieve discomfort and reduce temperature slightly.
Potential Complications
While fever generally supports immune function, it may cause complications in some populations:
- Febrile Seizures: A complication seen mainly in young children, often harmless but requiring monitoring.
- Dehydration: Due to increased sweating and respiratory water loss.
- Delirium and Confusion: Especially in older adults, high fever may lead to temporary cognitive impairments.
- Organ Stress: High fevers, if sustained, can strain vital organs, particularly in individuals with underlying health conditions.
In these cases, monitoring and immediate medical attention can help prevent further complications (Dinarello & Porat, 2020).
Prevention of Fever
Preventive measures primarily focus on avoiding infections and managing chronic health conditions that may predispose individuals to fever:
- Hand Hygiene: Regular hand washing to prevent infections.
- Vaccination: Helps prevent diseases like influenza and pneumonia, common fever causes.
- Avoiding Contaminated Sources: Particularly food and water sources in endemic regions.
Conclusion
Fever is a common symptom with a range of causes, from infections to immune responses. It plays a critical role in fighting infection, as the body’s elevated temperature can inhibit pathogen growth. Proper diagnosis involves physical examination, laboratory tests, and accurate temperature assessment. Treatment includes antipyretics, supportive care, and, if necessary, specific antimicrobial therapy for infections. Prevention focuses on hygiene, vaccination, and managing predisposing conditions. While fever itself is usually beneficial, monitoring is essential to avoid potential complications, especially in vulnerable populations.
References
Dinarello, C. A., & Porat, R. (2020). Fever in Infectious Diseases. In Mandell, Douglas, and Bennett’s Principles and Practice of Infectious Diseases, 9th Edition. Elsevier. https://www.sciencedirect.com/science/article/pii/B978032348255400039X
Harrison, T. R. (2022). Fever and Hyperthermia. In Harrison’s Principles of Internal Medicine, 21st Edition. McGraw-Hill Education. https://accessmedicine.mhmedical.com/content.aspx?bookid=2129§ionid=192012433
Mayo Clinic. (2023). Fever: Causes, Diagnosis, and Treatment. Mayo Clinic. https://www.mayoclinic.org